Feeling ready to take cybersecurity seriously? If you’re like 96% of business CEOs, you know that cybersecurity is a priority. A cybersecurity breach can have devastating consequences, including loss of data, financial loss, damage to reputation, and even legal liabilities.
You know you need to do something, you don’t need to be convinced of that. But as a business decision-maker, you can’t put the right safeguards in place until you have a comprehensive understanding of your IT environment.
This brings us to an essential starting point.
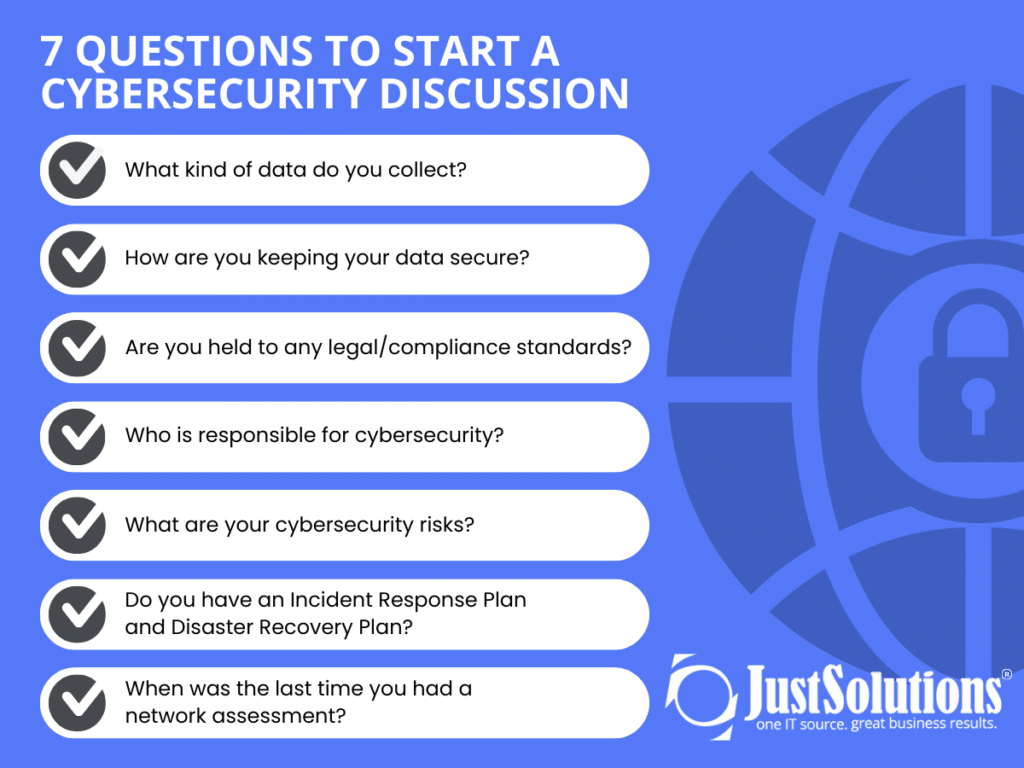
Here are 7 insightful questions that will help steer your cybersecurity discussion in the right direction.
#1) What Kind of Data Do You Collect?
Every business collects and stores some type of data. Your data consists of digital information that is important for business functions. The type and sensitivity of the data you handle will be dependent on your industry. But whether you’re an insurance agency, a law firm, or a retail shop your data is valuable and needs to be protected.
Before you figure out how to secure it, you need to know what you’re working with. It’s time to take inventory.
Here are some examples of data to take into consideration.
- Customer Information
- Financial Information
- Company Records
- Employee Information
Now that you’ve identified what kind of data you have, you should be aware of where all your data is stored. Is it located on a local hard drive, the cloud, or a remote server?
Understanding where you store your data is essential for maintaining control over your information, complying with legal and regulatory requirements, and making informed decisions about how to manage and use your data effectively.
#2) How Are You Keeping Your Data Secure
Be honest. What are you doing to keep your business data secure? There’s not one single security solution you should be using. Creating a secure environment requires a multi-layered approach. If you have any of these in place then you’re off to a good start.
- Security Tools
- Strong Password Use
- Multi-Factor Authentication
- A Secure Internet Connection
- Up-To-Date Infrastructure
51% of small businesses, don’t have any IT security measures. Don’t think that cybercriminals haven’t caught on. SMBs are an easy target due to the fact that many are not prepared to defend themselves.
#3) Are You Held to Any Legal/Compliance Standards?
Before you get too far in planning your cybersecurity strategy, make sure you’re aligned with any legal or compliance standards your business is under.
Various regulations require strict adherence to ensure data protection. Do you comply with relevant regulations like HIPAA, CMMC, the NY SHIELD Act, or others applicable to your industry? Check and make sure you’re on the right track.
If you’re considering buying cyber insurance in the future, keep in mind that insurance providers may also require certain precautions to be taken to qualify for coverage.
#4 Who Is Responsible for Cybersecurity?
As a SMB you probably don’t have a full team dedicated to security. However, you do need an individual who is going to lead your security initiatives. It could be your IT manager, you as a business owner, a CIO, or an admin.
Whoever it is, this person should manage your day-to-day security responsibilities. They will provide leadership and set employee expectations. This person should claim ownership of cybersecurity initiatives, but everyone plays a part.
As you develop a cybersecurity culture, everyone should take responsibility. Encouraging all departments within your company to participate in cyber hygiene practices is crucial for success.
#5) What Are Your Cybersecurity Risks?
The news is often filled with stories of cyber attacks. With so many threats out there, it’s tough to know which ones to focus on. Staying up to date with the latest cybersecurity trends can be incredibly helpful in identifying the most prevalent threats in your industry.
Are you well-versed with the potential threats to your business? Here are a few of the most common ones that SMBs are experiencing.
Phishing attacks: Phishing attacks are one of the most common types of cyber attacks, where cybercriminals send fraudulent emails or messages to trick employees into revealing sensitive information or downloading malware.
Malware attacks: Malware attacks involve the use of malicious software to gain unauthorized access to a business’s computer systems, steal data, or cause damage to the system.
Ransomware attacks: Ransomware is a type of malware that encrypts a business’s data, making it inaccessible, and demands payment in exchange for the decryption key.
Insider threats: Insider threats refer to the risks posed by employees or contractors who have access to sensitive data and systems. Human error accounts for over 80% of cyber incidents. These threats can be intentional or unintentional, and they can cause significant damage to a business’s reputation and finances.
Weak passwords: Weak passwords are a common security risk that allows cybercriminals to gain unauthorized access to a business’s systems or data.
To protect against these cybersecurity risks, businesses should implement strong security measures such as employee training, multi-factor authentication, regular data backups, and up-to-date antivirus software. It’s also important to regularly review and update security policies and procedures to ensure they are effective against emerging threats.
#6) Do You Have an Incident Response Plan and Disaster Recovery Plan?
Crossing your fingers isn’t enough when it comes to data protection and it certainly won’t help you recover from a disaster. Having a plan for when things go wrong ensures you can get back on your feet again.
What would you do if a disaster occurred? Disaster recovery plans and incident response plans are used by organizations to ensure business continuity in the event of a disaster, cyber attack, human error, power outage, or hardware failure.
- Incident Response Plan (IRP): A set of procedures and policies that an organization follows to detect, respond to, and mitigate an incident that could negatively impact its information technology infrastructure, such as a security breach, data leak, or virus outbreak.
- Disaster Recovery Plan (DRP): a set of procedures and policies that an organization follows to recover from a major disruption or disaster that affects its information technology infrastructure, such as a natural disaster, cyber-attack, or system failure.
While both the IRP and DRP serve to protect a company from potential threats, there is a fundamental difference between the two. IRP focuses on managing the incident as it happens, understanding how it occurred, and taking measures to prevent future occurrences. DRP, on the other hand, prioritizes how to recover from catastrophic events and maintain business continuity during and after a disaster.
#7) When Was the Last Time You Had a Network Assessment?
By conducting network assessments, you can thoroughly examine your systems and identify entry points that could be exploited. The assessment will also provide you with insights on how to minimize the risk of a potential attack. If you haven’t had a network assessment done in over a year, it’s highly recommended to reach out to a trusted company to schedule one as soon as possible.
To ensure your network is running smoothly, it’s advisable to evaluate it every quarter. For small businesses, once a year is the minimum. The frequency of assessments depends on various factors such as the complexity of your systems, infrastructure changes, and compliance requirements.
The following are the two primary categories of network assessments.
- Vulnerability Assessment: A vulnerability assessment identifies and analyzes security weaknesses in a system, network, or application. It then prioritizes these vulnerabilities and provides recommendations for remediation to enhance the organization’s security posture.
- Penetration Testing (pen-test): A penetration test is a simulated cyber attack against a computer system, network, or application to identify vulnerabilities that could be exploited by attackers. This practice is conducted by ethical hackers, who use the same techniques as cybercriminals but with the goal of uncovering and fixing security weaknesses rather than exploiting them.
Prioritizing Cybersecurity for Your Business
It’s no secret that cybersecurity is a pressing issue that business owners must address. To protect your business, customers, and stakeholders, it’s important to have an open discussion and take proactive measures to mitigate cyber threats.
Answering these questions is a great start to enhancing your security posture. The next step is to focus on the areas that make you vulnerable. Regardless of the size of your team, whether it be 10 or 100 employees, safeguarding your business is achievable. It’s not an overnight process, but investing in your security is definitely worth it.
For small business owners who may have limited time and resources, Just Solutions can help. As a managed IT service provider that specializes in security, we can identify vulnerabilities and ensure that your IT systems remain secure. Take the first step towards securing your network by scheduling a security assessment with us.

